Cybercriminals are deploying VCURMS and STRRAT Trojans via AWS and GitHub.
A new phishing effort has been discovered to deploy remote access trojans (RAT) such as VCURMS and STRRAT using a malicious Java-based downloader.
Microsoft fixes 61 vulnerabilities, including critical Hyper-V flaws, in its March updates.
“The attackers stored malware on public services like Amazon Web Services (AWS) and GitHub, employing a commercial protector to avoid detection of the malware,” Fortinet FortiGuard Labs analyst Yurren Wan stated.
One noteworthy component of the campaign is VCURMS’ use of a Proton Mail email address (“sacriliage@proton[.]me”) to communicate with a command-and-control (C2) server.
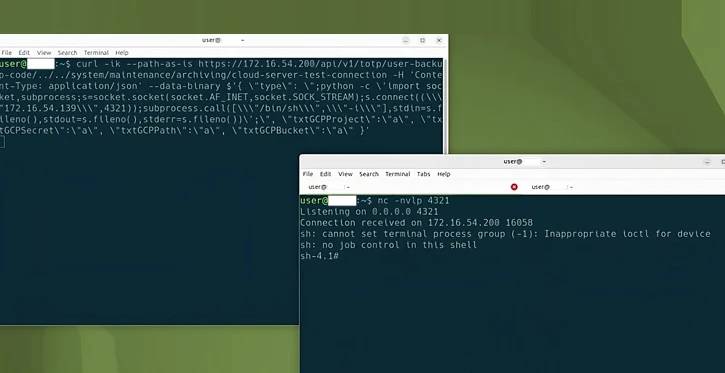
The attack chain begins with a phishing email that prompts recipients to click on a button to verify payment details, which leads to the download of a malicious JAR file (“Payment-Advice.jar”) located on AWS.
When the JAR file is executed, two more JAR files are retrieved and launched independently to activate the twin trojans.
Aside from sending an email with the phrase “Hey master, I am online” to the actor-controlled address, VCURMS RAT regularly scans the mailbox for emails with certain subject lines to extract the command to be performed from the content of the message.
This includes performing arbitrary commands using cmd.exe, obtaining system information, looking for and uploading relevant files, and downloading more information stealer and keylogger modules from the same AWS URL.
The information stealer is equipped with the ability to steal sensitive data from applications such as Discord and Steam, passwords, cookies, and auto-fill data from multiple web browsers, screenshots, and detailed hardware and network information about compromised hosts.
VCURMS is claimed to be comparable to another Java-based infostealer dubbed Rude Stealer, which appeared in the wild late last year. STRRAT, on the other hand, has been spotted in the wild since at least 2020, and is often distributed via bogus JAR files.
“STRRAT is a RAT built using Java, which has a wide range of capabilities, such as serving as a keylogger and extracting credentials from browsers and applications,” Wan said in a blog post.
Thousands of Roku accounts were compromised in a credential stuffing an attack.
The news comes after Darktrace identified a unique phishing effort that uses automated emails sent from the Dropbox cloud storage service via “no-reply@dropbox[.]com” to spread a fraudulent link that looks like the Microsoft 365 login page.
“The email itself contained a link that would lead a user to a PDF file hosted on Dropbox, that was seemingly named after a partner of the organization,” the business stated in a statement. “the PDF file contained a suspicious link to a domain that had never previously been seen on the customer’s environment, ‘mmv-security[.]top.'”