Vendors of a novel utility that weaponizes the Raspberry Pi
Threat actors developed Geobox, a novel solution that turns the Raspberry Pi, a mini-computer, into a hacking tool similar to a Swiss army knife, which fraudsters and other offenders use.
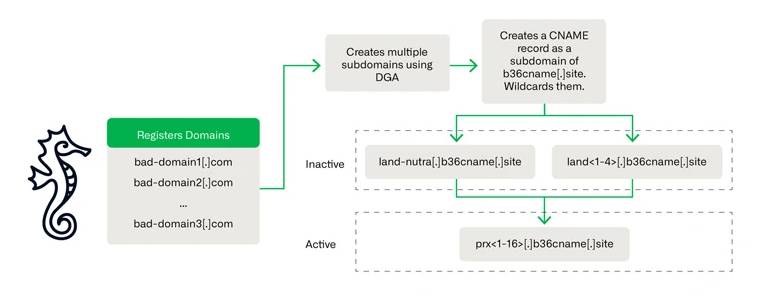
The software, which can provide anonymity while spoofing location, imitating Wi-Fi access points, and manipulating DNS and network parameters, is available for a lifetime charge of $700 or a monthly rate of $80.
While investigating the online banking larceny of a high-net-worth client, Resecurity researchers discovered discussions regarding the new tool on Telegram and the Dark Web.
OpenAI recently developed a ‘Voice Engine’ that can clone speech in less than 15 seconds.
The malevolent actors strategically positioned a multitude of Geobox devices in various remote areas and connected them to the internet. By functioning as proxies, these devices substantially augmented their level of anonymity. Their report states, “This approach complicated the investigation and tracking process, especially considering that Geobox devices do not store logs by default.”
The Raspberry Pi is an all-purpose, inexpensive, and diminutive single-board computer that is lauded by devotees and utilized in a variety of endeavors. On the contrary, Geobox renders it “a formidable instrument for digital deception.” Developers have developed malicious software specifically for the Raspberry Pi 4 Model B, a device that requires a minimum of 4GB of RAM.
Due to the setup process’s simplicity, clarity, and succinctness, along with its straightforward instructions, malicious actors use Geobox to target a wide-ranging audience. For OS installation, the manual provides a link to the official Raspberry website.
Geobox includes many tools such as multiple VPN connections, GPS and Wi-Fi emulation, DNS configuration, data substitution tools, and network configurators.
“The device exhibits a wide range of functionalities, enabling it to execute diverse types of digital manipulation and disguise.” Significant features include the ability to use WebRTC IP for secret electronic communication and GPS deception to fake different geographic locations, making it very useful for tasks that need to change geolocation. Additionally, by masking Wi-Fi MAC addresses, the Geobox obfuscates the user’s network activity, thereby augmenting the difficulty of tracing it. Resecurity reported.
The advent of Geobox brings forth substantial apprehensions and introduces novel intricacies within the realm of cybersecurity.
Equipped with this instrument, cybercriminals possess the capability to execute and orchestrate a multitude of assaults, including but not limited to credit card fraud and identity theft conducted anonymously, circumventing network restrictions and surveillance, distributing malware, inserting credentials, disseminating false information, and pirating content.
Bitcoin hosts approximately $70,000, but meme coins dominate.
Resecurity identified the malevolent individual as using Geobox in conjunction with two LTE-based wireless modems to “proxy connections through multiple chains of SOCKS and PROXY servers.” The utilization of this model across multiple devices situated in diverse locations could pose a formidable obstacle in the pursuit of cybercriminals employing it.
“After carrying out the malicious action, we either delete or physically destroy the device before relocating it.”